 Imagine for a moment that someone burgles your house, steals some electronic equipment, and then phones you a couple of weeks later to ask if you’ve got the manuals for it. (actually, fans of British sitcoms may well recognise this from a “One Foot in the Grave” episode).
Imagine for a moment that someone burgles your house, steals some electronic equipment, and then phones you a couple of weeks later to ask if you’ve got the manuals for it. (actually, fans of British sitcoms may well recognise this from a “One Foot in the Grave” episode).
That’s what TechCrunch’s statement that they’ve “spent much of the last 36 hours talking directly to Twitter about the right way to go about [posting the stolen documents]” feels like.
Now we know that TechCrunch didn’t steal them, and that the person who did decided to pop the docs in a virtual scatter gun, and that TC has milked and got a lot of mileage out of what are essentially fairly boring internal memos, but it once again raises an interesting question on what’s fair game to publish.
In fact, TechCrunch (and a number of other organizations) do this on a regular basis, on the premise that, while “many users say this is ‘stolen’ information and therefore shouldn’t be published, we disagree.”
Breaking embargo is far from a problem (despite the wrath of some PR companies) but I don’t buy Arrington’s “I feel bad for Twitter and I wish this had never happened”.
Trash the faux remorse and the “we’ve been sitting in the office for eight hours now debating what the right thing to do is in this situation”. We all know this is what TC does because it’s big and ugly enough to get away with it (as are many others).
Of course you’re glad it happened, Michael, because it’s raised your own profile. Heck, even I’m linking to you.
“We don’t sit around and republish press releases, we break big stories.”
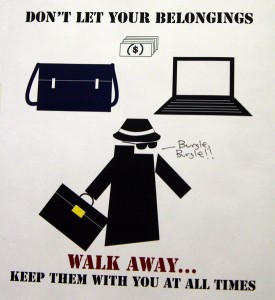
The real moral of the story is that organizations need to take a long hard look at, and then fix, their security, because there’s very little that remains unpublishable these days.
Originally posted on July 17, 2009 @ 5:39 am